GDPR
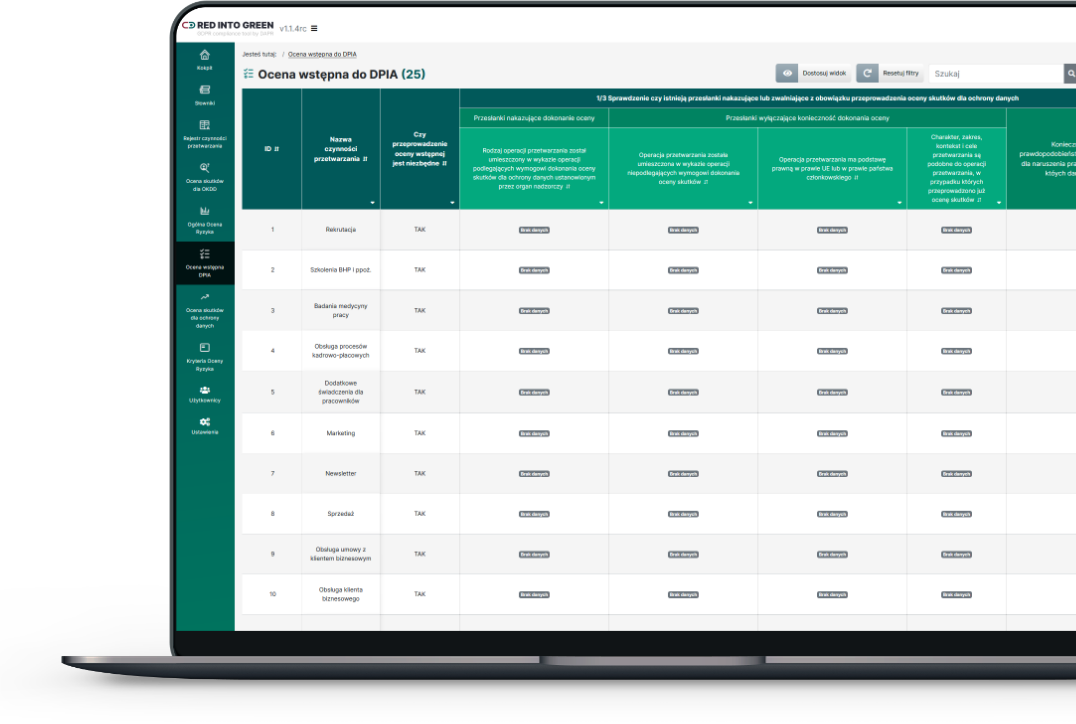
According to the GDPR, the risk-based approach should be the foundation of personal data protection. That is why it is our primary focus when working with clients. Once we carry out a thorough risk analysis, the rest is easy. We can provide GDPR-compliant methodology and a risk analysis app. We can teach your team how to do such analyses on their own. If you wish, we can conduct a GDPR-related risk assessment for you and show you the results in a detailed report. For our clients we also carry out selective analyses of individual processes linked with the “privacy by design” principle set out in the GDPR. Naturally, we also take care of DPIAs and evaluate processing activities for those assessments. Our advantage lies in carefully crafted risk analysis methodology, supported by our own Red Into Green software as well as years of experience from projects and training courses. You can read about the organizations which have trusted us with risk analyses in the “About us” section and on the Home page.
AML
Client risk analysis along with AML/CFT risk identification and assessment are essential obligations imposed by the countering money laundering model. How can we help you in this regard? We will be happy to create potential money laundering scenarios for your organization; we will teach you how to carry out a risk analysis and we will provide you with relevant tools. We can also do such an analysis for you. We have developed a tool enabling our clients to conduct an analysis on their own. What else? Once we have the analysis ready, we can set up procedures and documentation required by the law.
Whistleblowers
We carry out audits of existing systems for submitting notifications, including post-audit reports and presentations for executive teams. We identify notification channels and prepare full documentation including templates for: bylaws and procedures, contracts with providers (we can also evaluate them), authorisations, NDAs and records. We hold training courses for executive teams, people designated to receive notifications as well as other staff.
IT support
We provide comprehensive support – from identifying client needs to optimising purchases to designing effective workstations. We can carry out a simulation of an attack on your business in order to check your weak spots and to raise employee cyber security awareness.